On March 31, 2026, security researcher and Fuzzland co-founder Chaofan Shou disclosed an extremely rare code security incident. Anthropic The Official Command Line Intelligent Body Assistant Claude Code A full source code leak has occurred.
The raw, unobfuscated code is now spreading like wildfire in the developer community. Anyone can easily access the engineered source code of this AI intelligence, which represents the best in the industry.
Fatal Configuration Errors and the State of Source Code Acquisition
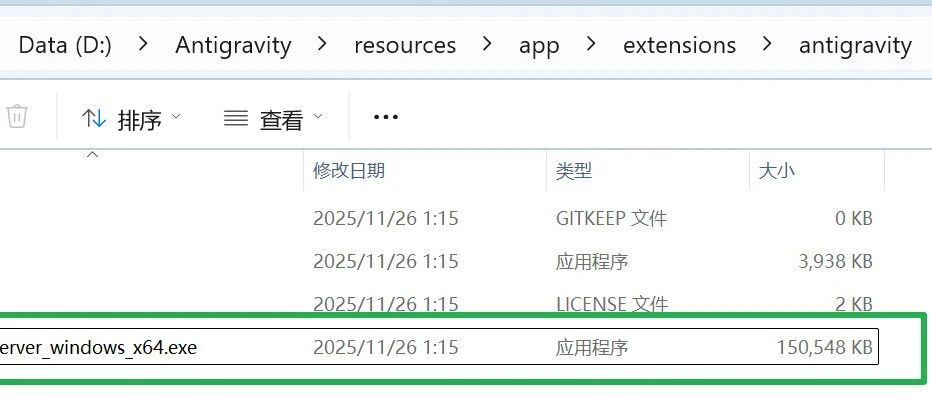
The incident stemmed from a low-level configuration error in front-end engineering. The Anthropic development team, when publishing the CLI toolkit to the npm registry, failed to include the .map Source mapping files are added to the ignore list. This results in files containing full unobfuscated TypeScript source references being directly packaged for public consumption.
After installing the tool locally, the developer found that the generated .map The file exposes a direct URL to Anthropic's internal Cloudflare R2 storage bucket. resolving this link allows anyone to directly download a zip archive containing the entire project source code.
The most complete leaked code has now been backed up to the GitHub platform:
- Full source code backup repository: https://github.com/instructkr/claude-code
Status and boundaries of source code snapshots
A large number of developers have cloned the repository and found that the current library only retains the core src/ Catalog tree. It is missing the usual top-level project metadata, including the package.json , dependency lock files, build scripts, test commands, and a clear release directory structure.
This means that the current repository cannot be directly installed or run with a single click. It's better thought of as an invaluable code-reading and architectural reference snapshot. It also shows that Anthropic has built an extremely complex internal packaging and distribution process.
Panoramic overview: it's not a simple wrapper
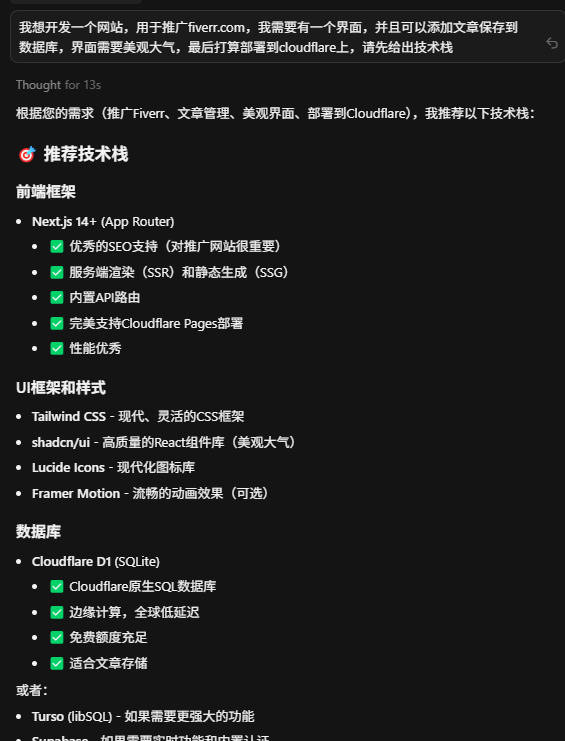
Claude Code is far more than just a flat CLI command-line wrapper. It's a complete tool-centric application runtime built around the following capabilities at its core:
- Interactive CLI experience with a large built-in command surface
- Expose the runtime of files, shells, web, tasks, and smartbody tools
- Support for local and remote execution streams
- for tool interoperability MCP Server Entry
Core code disassembly: seven-tier application architecture
Diving into these 512,000 lines of TypeScript code, it's clear to see that it's divided into seven logical architectural layers.
Layer 1: process entry and mode of operation
The startup path for the CLI is centralized in the src/main.tsx 和 src/entrypoints/cli.tsx The boot design has two goals. The boot design has two goals: to support multiple modes of operation and to make common boot paths extremely responsive.
It does this by parsing the arguments against the --version The system provides fast paths to commands such as the MCP, and uses delayed loading to avoid introducing all the modules at once. The system not only provides a regular interactive terminal, but also supports MCP server mode, non-interactive printing, background daemons, and remote bridges.
Layer 2: Command routing system
The command layer is located at the src/commands.ts 及 src/commands/ Catalog. The user-visible input intents are defined here, and the source code exposes nearly 50 commands. Covering authentication login, code review ( /review ), comparison of differences ( /diff ), contextual compression ( /compact ), persistent memory management ( /memory ), MCP management and even remote environmental transport.
Layer 3: Session Engine and Single Round Cycle
This layer is the heart of the system and is architected with a fine-grained segregation of duties:
src/QueryEngine.ts: Acts as the owner of the conversation. It keeps a history of messages across multiple rounds of conversations, a cache of file reads, Token Consumption statistics, and management authority to reject records.src/query.ts: Responsible for the underlying single-round execution loop. It handles model response flow, articulation of tool calls, automated and responsive context compression, and recovery logic when Token hits its upper limit.
Tier 4: Tool systems
In Claude Code, tools are first class citizens. Every tool call is made in the src/Tool.ts defined ToolUseContext runs in the application state read/write interface, MCP resources, and privilege hooks. src/tools.ts About 40 tools controlled by feature switches have been registered. These include Bash execution, file read/write replacement, Notebook editing, web crawling, and team-level sub-intelligence generation tools.
Layer 5: Task
The system makes a clear distinction between “tools” and “tasks”. Tools are one-time capability calls, while src/Task.ts A defined task is a traceable execution unit with a life cycle (waiting, running, completed, failed, terminated). src/tasks.ts registers local shell jobs, local and remote intelligences to perform tasks, and even includes a new program called dream of background idle organizing tasks.
Layer 6: Interactive State and UI
The terminal interface is far from simple plain text output. src/state/AppStateStore.ts Demonstrates an extremely broad coverage of React State Model. It tracks setup parameters, MCP client resources, to-dos, the thinking state of the model, and the UI state of the remote bridge. Terminal command input is the same as src/components/ Deep coupling is achieved by rendering a large number of Ink components under the
Layer 7: Services, Bridging and External Integration
The real business orchestration is dispersed in this layer:
- Services and infrastructure:
src/services/和src/utils/Includes analytical telemetry, contextual compression engine, policy limits and team memory synchronization. - Remote and Bridge: Independent subsystems
src/bridge/Handles remote session URL compatibility, trusted device workflows, and bi-directional transfers. - MCP Integration:
src/entrypoints/mcp.tsServes as a core entry point that allows external clients to discover and invoke internal system tools via the stdio transport protocol.
Privilege, Security and Feature Switches
Security constraints are a central part of the system runtime. The code in the ToolPermissionContext It is shown that the tool execution is naturally policy-aware. Different modes of operation (local, remote, headless) dynamically change permissions behavior, and some background tasks are even forcefully configured to disable pop-up authorization.
The code base is extensively covered with feature('...') Feature switch judgment. This means that inactive features are trimmed at compile time and the current source snapshot actually contains a superset of multiple product variants.
Deep analysis: end-to-end flow of a single request
By tracing the source code, a complete single request execution path is as follows:
- The process is started from the CLI or a specific portal.
- The startup logic selects the mode of operation and initializes the configuration, authentication and policy state in parallel.
- The system assembles the commands and tools registry for the current session.
- Create an interactive AppState in interactive mode.
- The user enters a command or message.
QueryEngineAssembling single interactions with session-level execution contexts.- go into
query.tsof flow circulation pipes. - model output text, or trigger a tool-use tool call request.
- The system validates and executes tools according to the internal tool contract and permission system.
- The results of the tool execution are re-merged into the message stream.
- UI components, task state, and session state are synchronized and updated.
- Loop to determine if it completes, compresses the context, or performs a failure retry.
Read this professional guide to 510,000 lines of source code
Faced with such a large code base, analysis requires a specific strategy.
Developer's reading path:
It is recommended that the habit of looking from the bottom up be discarded and the following order be used:
Check the entry registry first src/main.tsx 与 src/commands.ts ; proceed to understand the core abstraction src/Tool.ts 、 src/tools.ts 、 src/Task.ts 和 src/tasks.ts Subsequent penetration into the central nervous system src/QueryEngine.ts 和 src/query.ts ; looking again at state management src/state/AppStateStore.ts and the MCP portal src/entrypoints/mcp.ts . Finally, based on interest in exploring src/bridge/ 和 src/services/ 。
Retrieval strategies designed for AI agents:
When analyzing the repository, the AI should prioritize the registry before looking for specific implementations. Analyze “what capabilities” separately from “how they are implemented” and explicitly track Feature Gate variables. Effective entry points include tracing the complete path of a tool from registration to execution, distinguishing between the Tool and Task data models, locating the Session State owner, and exploring how the MCP server calls internal tools.
The hidden secrets of community digging
After patching the complete code structure, the developers used the feature switches to extract yet-to-be-released internal functionality.
There is an unreleased KAIROS daemon embedded in the system. When activated, the assistant becomes a daemon resident in the background, actively listening to the GitHub Webhook and taking over multiple parallel sub-intelligences.
For Anthropic's internal employees, the code forces an “undercover mode”. When an employee is detected operating in a public warehouse, the system automatically wipes out all AI-generated traces and tampers with prompts to conceal their identity.
The development team also hid an electronic pet system containing 18 settings deep in the code, utilizing string functions to circumvent scanning. The underlying telemetry module not only monitors crash logs, but also accurately counts the frequency of profanity entered by users to assess the model's usability metrics.